NANOG 88

Chat with NANOG 88 attendees!
Open Chat WindowWatch the Webcast
Watch Now- Events
- NANOG 88

Thank you for joining us in Seattle, WA
for NANOG 88
Our 88th community-wide gathering was 12-14, June, 2023.
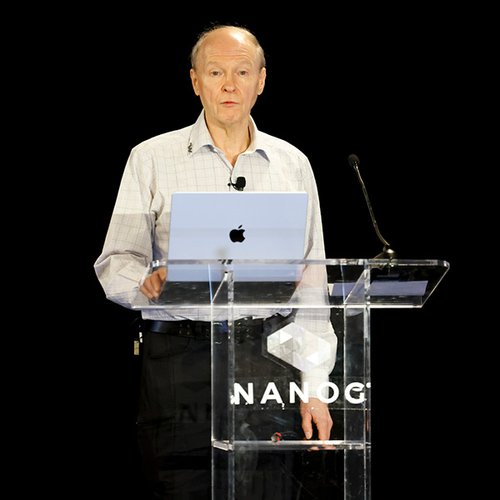
KEYNOTE | From Data Links to Internets: A Quick Tour
Speaker: Len Bosack
From concept to equipment needs to various attempts to today, Bosack provides insight into the path of getting from the initial data links before the Internet to the commercial Internet the world has come to know.

NANOG 88 Hotel Information
Headquarter Hotel
Hyatt Regency Seattle
808 Howell Street
Seattle, Washington 98101

Social Events
Our community is what makes NANOG special. Check out our past daily social events during NANOG 88!

Can You "Dig" It?
Exploring the Fundamentals of DNS
This 1-Day Course explored the history of the Domain Number System (DNS), the original design, how it works, and its evolution. Presented by Eddy Winstead.

NANOG 88 Agenda

Start your day the healthy way!
Free yoga in Seattle
Monday, Tuesday & Wednesday mornings
Limited to 10 students per day
All levels are welcome